Small businesses are prime targets for cyberattacks. Hackers know that while large corporations have dedicated security teams, small businesses often have limited resources and less sophisticated defenses.
In fact, according to recent studies, 43% of cyberattacks target small businesses, and 60% of small companies go out of business within six months of a cyber breach.
The good news? Most breaches are preventable. After responding to countless security incidents, I have identified five critical mistakes that leave businesses vulnerable—and how to fix them.
Mistake #1: Weak or Reused Passwords
The Problem: Employees using simple passwords like “Password123” or reusing the same password across multiple accounts creates an open door for attackers.
When one account is compromised (which happens frequently with data breaches), hackers can access every other account using the same credentials.
The Fix:
- Implement a password manager for your entire team (LastPass, 1Password, Bitwarden)
- Require passwords to be at least 12 characters with a mix of letters, numbers, and symbols
- Enforce password rotation every 90 days
- Enable multi-factor authentication (MFA) on all business accounts
Real-world impact: MFA alone blocks 99.9% of automated attacks, according to Microsoft.
Mistake #2: No Regular Software Updates
The Problem: Outdated software is one of the easiest entry points for hackers. When security vulnerabilities are discovered, software vendors release patches—but those patches only work if you install them.
Delaying updates because “we are too busy” or “we will do it next week” gives hackers time to exploit known vulnerabilities.
The Fix:
- Enable automatic updates for operating systems and software
- Prioritize critical security patches and apply them immediately
- Maintain an inventory of all software and hardware
- Phase out end-of-life software that no longer receives security updates
Example: The 2017 WannaCry ransomware attack exploited a Windows vulnerability that Microsoft had patched two months earlier. Organizations that had not updated were crippled.
Mistake #3: Inadequate Employee Training
The Problem: Your employees are your first line of defense—and often your weakest link. Phishing emails are getting more sophisticated, and one click on a malicious link can compromise your entire network.
Most employees do not realize they are making security mistakes until it is too late.
The Fix:
- Conduct quarterly cybersecurity training for all employees
- Run simulated phishing attacks to test awareness
- Teach employees to recognize red flags:
- Unexpected urgent requests
- Suspicious email addresses
- Links that do not match the display text
- Requests for sensitive information
- Create a clear incident reporting process so employees know what to do if they suspect a threat
Remember: Human error is responsible for 95% of cybersecurity breaches. Training is not optional—it is essential.
Mistake #4: No Data Backup Strategy
The Problem: Ransomware attacks are on the rise, and they are targeting small businesses. When ransomware encrypts your data, you have two choices: pay the ransom (with no guarantee you will get your data back) or restore from backups.
If you do not have backups, you are out of business.
The Fix:
Follow the 3-2-1 backup rule:
- 3 copies of your data (original + 2 backups)
- 2 different media types (local hard drive + cloud storage)
- 1 offsite backup (cloud or remote location)
Additionally:
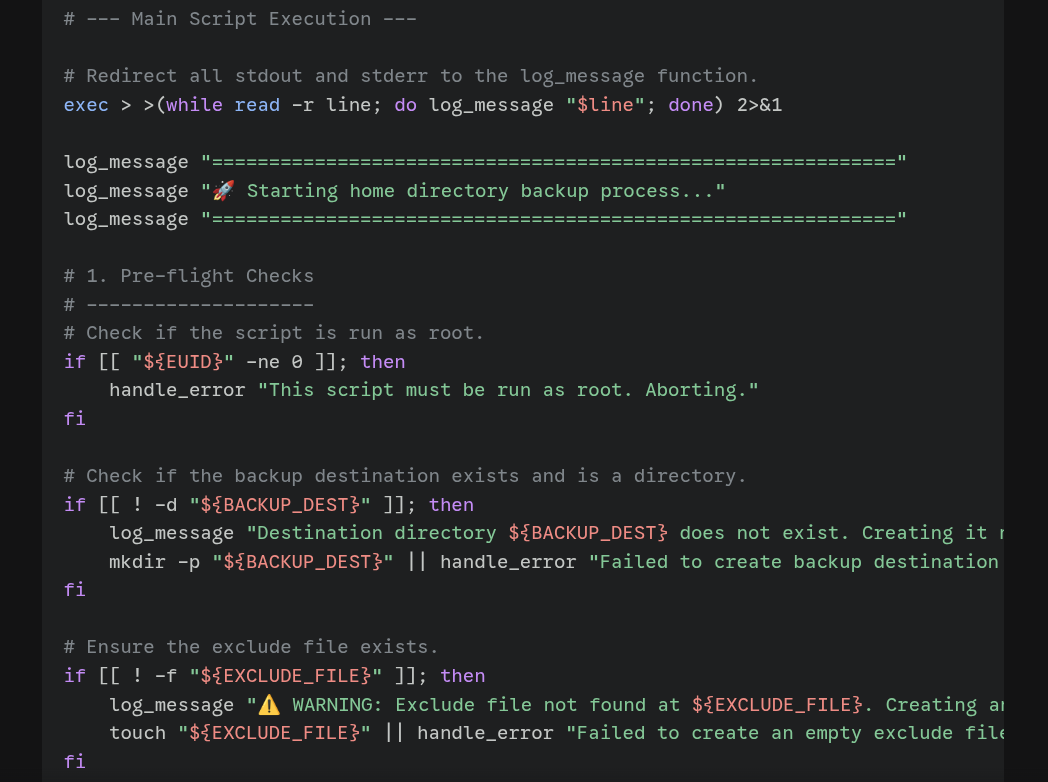
- Automate daily backups
- Test restore procedures quarterly
- Keep backups air-gapped (disconnected from your network) to prevent ransomware from encrypting them
- Maintain versioned backups (not just overwriting the same backup)
Real-world scenario: A client was hit with ransomware that encrypted their entire file server. Because they had offsite backups, they were back up and running in 4 hours instead of paying a $50,000 ransom.
Mistake #5: Unsecured Remote Access
The Problem: The shift to remote work has created new vulnerabilities. Many businesses set up remote access quickly without proper security measures, leaving backdoors open for attackers.
Remote Desktop Protocol (RDP) attacks have skyrocketed, with hackers scanning for exposed RDP ports and brute-forcing passwords.
The Fix:
- Never expose RDP directly to the internet
- Use a Virtual Private Network (VPN) for remote access
- Implement Zero Trust architecture (verify every access request, even from inside the network)
- Require MFA for all remote connections
- Use endpoint security software on all devices (company-owned and BYOD)
- Monitor for unusual login attempts or access patterns
Bonus tip: Consider using a Remote Desktop Gateway or secure access solution like Cloudflare Access, Azure AD, or similar.
The Cost of Inaction
These mistakes might seem minor, but the consequences are severe:
- Average cost of a data breach for small businesses: $200,000
- Average ransomware payment: $170,000 (and climbing)
- Downtime costs: $5,600 per minute for critical systems
- Reputation damage that can take years to rebuild
Take Action Today
Cybersecurity does not have to be overwhelming. Start with these five areas, and you will be ahead of 80% of small businesses.
Quick Action Checklist:
- Enable MFA on all business accounts this week
- Schedule automatic software updates
- Set up employee security training for next month
- Verify your backups are working (test a restore)
- Review and secure remote access methods
Need Help Securing Your Business?
At Rainier IT, we provide comprehensive cybersecurity assessments and managed security services for small and medium businesses. We will identify your vulnerabilities, implement proven security measures, and provide ongoing monitoring to keep your business protected.
Schedule a free security assessment to find out where you stand and what steps you need to take to protect your business.