One of the most common questions we get: what’s the difference between the antivirus built into Windows and the extra security tools we recommend? The short answer is Huntress Managed EDR, and the long answer is below: first in plain English, then under the hood for the technically curious.
🛡️ Why this isn’t optional anymore
Cybersecurity guides love big numbers, but the ones that actually matter for a small business are the ones that show up on a cyber-insurance renewal. Here’s the 2026 reality, pulled from the same sources we hand to our clients’ insurance carriers:
- 88% of SMB breaches in 2025 involved ransomware — versus 39% at large organizations. Small businesses are the target, not collateral damage. (Verizon 2025 DBIR, SMB Snapshot)
- $115,000 median ransom payment in 2025 — before recovery, downtime, or legal costs. (Verizon DBIR)
- 81% of SMB ransomware claims involve operational shutdown — not just data loss, lost revenue. (NetDiligence 15th Annual Cyber Claims Study, n=10,402)
- $84,000 average ransomware claim for businesses under $25M revenue. Small enough to feel real. Large enough to be fatal. (Coalition 2025 Cyber Claims Report)
- 82% of denied cyber-insurance claims lacked basic MFA and EDR. The same controls that prevent breaches are the ones that get claims paid. (Coalition 2024 data, via Marsh McLennan, Aug 2025)
That last one is the kicker: even when something is covered, carriers are denying claims when the basics aren’t there. EDR — the kind of EDR a real human watches 24/7 — is on every modern insurance application. Huntress is how we say yes to that question without flinching.
What is “EDR,” and how is it different from antivirus?
Old-school antivirus is a bouncer at the door. It checks every file against a list of known troublemakers (signatures). If the file’s name and fingerprint are on the list, it gets turned away. Useful — but it only catches threats that have already been seen and catalogued. A new variant, an obfuscated payload, or an attacker using your own legitimate tools against you (PowerShell, Microsoft Office macros, scheduled tasks) walks right in.
EDR — Endpoint Detection & Response — is a security camera with a guard watching the feed. Instead of just checking the door, it watches what processes do after they’re running. A program that quietly creates a registry key to launch itself at boot. A spreadsheet macro that spawns PowerShell. A scheduled task added at 2 a.m. on a Saturday. None of these are necessarily “a virus” — but together they’re a hacker’s playbook, and EDR catches the pattern.
Managed EDR means there is a real human on the other end of that camera feed. That’s the part that matters most for a small business: you do not need a security analyst on staff. Huntress provides one — actually, a whole 24/7 team of them — for less than what one would cost you for a single afternoon.
What Huntress actually does for you
There are three pieces, and they all run quietly in the background:
1. A lightweight agent on every PC and server
It installs in seconds, uses negligible resources, and starts collecting the specific kinds of activity that hackers leave behind. It is not flashy — there is no big icon in your system tray, no scary popups, no “your computer is at risk!” nags. It is invisible until something is actually wrong.
2. A 24/7 team of human security analysts in Maryland (and around the globe)
This is the part competitors can’t fake. When the agent sees something suspicious, it gets escalated to a real Huntress security analyst — within 8 minutes on average (the industry standard is hours, sometimes days). They investigate, confirm whether it’s a real attack, and either remediate it for you with a single click or send a plain-English report explaining what to do next. False positive rate is under 1% — meaning when Huntress sends a ticket, it’s almost always real, so we (and you) don’t get alert-fatigued.
3. Ransomware tripwires, identity protection, and security awareness training
On top of the EDR core, Huntress quietly drops canary files across your endpoints — fake decoy documents that look like “Q4-Financials.xlsx” but exist only to get encrypted first. The moment one of them is touched, the SOC knows ransomware is running and starts isolating the machine — often before the attacker finishes encrypting the actual share. Their Managed ITDR service watches your Microsoft 365 logins for the same kinds of attacks (stolen tokens, malicious OAuth apps, hidden mail-forwarding rules). And their Managed Security Awareness Training sends bite-sized phishing simulations and three-minute training videos to your team every month — the same training your insurer is asking you to provide.
🔬 Now the technical part
If you stopped reading at the end of the last section, you have the gist. If you want to know how Huntress finds things antivirus misses, keep going.
How the agent decides something is suspicious
Huntress’s core EDR engine, called Process Insights, watches every process at creation time and maps its behavior against the MITRE ATT&CK Framework — the industry-standard catalog of every known attacker technique. It does not rely on file hashes or signatures, which is why it catches zero-days and heavily obfuscated payloads that traditional AV misses entirely.
On top of that, the agent collects targeted telemetry from the exact places attackers love to hide for long-term access — what the security industry calls persistence mechanisms. There are roughly a dozen common ones, and Huntress watches all of them:
- Registry Run keys — the autostart locations under
HKCU\and a half-dozen siblingsSoftware\ Microsoft\ Windows\ CurrentVersion\ Run - Scheduled tasks — created via
schtasks.exe, often with innocent-looking names likeGoogleUpdateTaskMachineCore - Windows services — installed via
sc createor PowerShell, configured to run as SYSTEM - Browser extensions — modern attackers ship malicious Chrome/Edge extensions that exfiltrate session cookies
- WMI event subscriptions — fileless persistence that survives reboots and most cleanup tools
- DLL search-order hijacks, BITS jobs, AppInit DLLs, IFEO debuggers, and several more obscure techniques
Here’s an example of what an attacker plants and what Huntress sees on the next agent check-in:
# Adversary plants a Run key — survives reboot, no file dropped
$payload = "powershell -nop -w hidden -enc <base64>"
New-ItemProperty `
-Path "HKCU:\Software\Microsoft\Windows\CurrentVersion\Run" `
-Name "OneDriveSync" ` # blends in with real Microsoft entries
-Value $payload -PropertyType String -Force
# Huntress collects this exact registry path on every check-in.
# An analyst sees "OneDriveSync" pointing at encoded PowerShell → ticket opens.Antivirus would not flag this — there is no malicious file on disk. PowerShell is a legitimate Windows tool. The Run key is a legitimate Windows feature. Only by collecting that specific registry path and letting a human (or a model trained by humans) look at the value would you ever notice the encoded payload pointing somewhere it shouldn’t.
Ransomware Canaries: the tripwire model
Most security tools try to detect ransomware by recognizing the malware itself. That is a losing arms race — there are dozens of new ransomware families per quarter and any of them can recompile in an afternoon to evade signatures. Huntress takes a different angle: detect the behavior, not the binary.
On every protected endpoint, Huntress drops small, hidden, lightweight files into directories ransomware typically targets first — Documents, Desktop, network shares. They look like ordinary documents but are watched continuously by the agent. They have three states:
- Armed — successfully deployed, monitored, untouched
- Pending — queued to be placed on a newly-onboarded endpoint
- Tripped — modified, renamed, or deleted (i.e., a ransomware operator just hit them)
The instant a canary is tripped, the agent fires an incident report to the SOC, who confirm whether it’s real ransomware (and not, say, you running a backup tool that touched the file). If it’s real, isolation begins:
# Ransomware encrypts everything it can see, including our tripwires
$ tree -L 1 ~/Documents | head
├── ImportantFile.docx.locked ← encrypted by ransomware
├── budget-2026.xlsx.locked ← encrypted by ransomware
└── .huntress_canary_4f3a.txt.locked ← canary file modified
# The Huntress agent notices the canary changed → SOC opens an incident
# within minutes — usually before the operator finishes encrypting the share.This works because ransomware operators don’t read the file system carefully — they recursively encrypt everything they can. The same blunt-force behavior that makes ransomware destructive also makes it impossible to avoid the canaries. By the time the operator finishes the run, the SOC has been alerted and is already pulling the network plug.
Managed ITDR: identity is the new endpoint
Huntress’s biggest 2025 expansion was Managed ITDR — Identity Threat Detection & Response — which extends the same SOC model to your Microsoft 365 tenant. The reason is simple: in 2026, attackers don’t break into your laptop, they steal your session token and log in as you from somewhere else, bypassing MFA entirely. Endpoint EDR can’t see that. ITDR can.
It runs three detection engines in parallel:
- Unwanted Access — account takeovers, impossible-travel logins, VPN-laundered sessions, session hijacking
- Shadow Workflows — malicious inbox rules and mail forwarding (the #1 BEC technique: silently forward all mail with the word “invoice” to attacker.com)
- Rogue Apps — malicious or risky OAuth applications that piggyback on legitimate consent flows (industry-first capability — Huntress analyzed over 20 million OAuth apps to build the baseline)
This is what a Rogue App actually looks like in your tenant — the kind of permissions you’d never knowingly grant, attached to an app with a name that pattern-matches something you trust:
{
"appDisplayName": "Adobe Acrobat Sign for Outlook", // looks legit
"publisherName": "free-mail-tools-llc", // it's not
"consentType": "AllPrincipals", // org-wide consent
"scopes": [
"Mail.ReadWrite", // read AND modify every inbox
"Mail.Send", // send mail as any user
"MailboxSettings.ReadWrite", // create stealth forwarding rules
"offline_access" // refresh tokens forever — no re-auth
],
"addedBy": "[email protected]",
"addedAt": "2026-04-29T03:14:07Z"
}Across 1.7 million identities under management, Huntress has stopped over 28,000 identity-based attacks with a mean time to respond under 3 minutes. For a small business, that is the difference between “the SOC isolated the account before the attacker sent a wire-transfer email” and “our bookkeeper just paid a fake invoice for $40,000.”
Why this beats “we already have antivirus”
Three things separate Huntress from the security stack you may already be running:
- It assumes the attacker is already inside. Traditional AV asks “is this file bad?” Huntress asks “does this behavior look like an attacker who’s already past the door?” That model catches insider threats, supply-chain compromises, and credential-theft attacks that bypass prevention entirely.
- The SOC is not optional or upsell. Many EDR products technically include “managed” tiers but ship as software-only by default. Huntress is the opposite — it is only sold managed. There is no tier where you’re staring at alerts alone at 2 a.m. The 24/7 SOC is the product.
- The false positive rate is genuinely under 1%. Real-world MSP reviewers consistently report “under 1 minute” to reach a human Huntress analyst. Compare that to the typical EDR experience of drowning in low-confidence alerts that nobody triages, until one of them was actually real.
Huntress won the 2026 SC Award for Best Managed Detection and Response Service and holds a 98.6% customer satisfaction score on Gartner Peer Insights. None of which would matter if it didn’t work — but it does, repeatedly, in real-world incidents on real client networks (including ours).
How we ship it
Huntress Managed EDR is an Authorized Partner product for Rainier IT — meaning we deploy and manage it on every plan that ships with 24/7 SOC:
- Small-business flat-rate plans: included on Business Shield ($199/mo) and Business Fortress ($349/month)
- Per-user plans: included on Co-Managed, Managed Pro, and Enterprise tiers
- Standalone: $25/endpoint/month for clients who want EDR without a managed plan.
- Add-on for Business Watch: $5/endpoint/month — the cheapest way to get Huntress on a small-business plan without jumping to Shield.
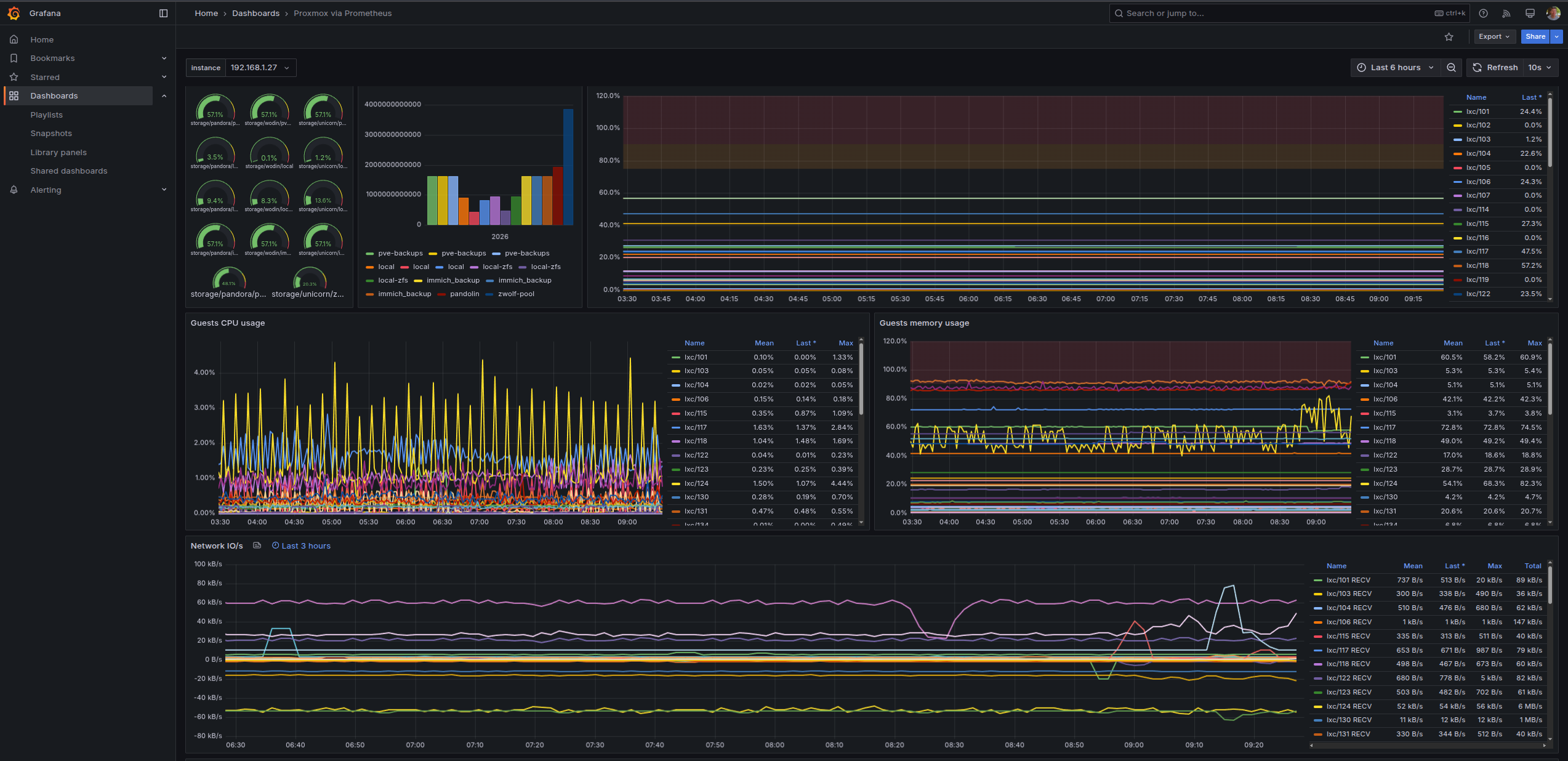
On every deployment we pair Huntress with a CIS-hardened Microsoft Defender baseline (16 ASR rules, BitLocker, Windows LAPS, no standing local admin), pushed via TacticalRMM and Action1, drift-corrected weekly. Defender does the prevention work it’s good at; Huntress does the detection-and-response work that prevention alone can’t cover. Together, that’s the security baseline your insurance carrier is asking for — and the one we’d want on our own machines if we were buying for ourselves. (We are. We do.)
Questions? Get in touch, or schedule a 30-minute call. We can pull a sample Huntress report from a real (anonymized) incident on a real network and walk you through what the SOC actually saw and did.
Stay safe out there.
— Christopher