What's the difference between Endpoint Hardened and Cloud Hardened?
Endpoint Hardened is everything we push to your Windows machines directly: Microsoft Defender at CIS Benchmark Level 1, 16 Attack Surface Reduction (ASR) rules, BitLocker full-disk encryption with keys escrowed in our RMM, Windows LAPS with rotating local-admin passwords, and no standing local admin. It works on any Windows endpoint, with or without Microsoft 365. Cloud Hardened adds the identity-layer controls — Conditional Access MFA, blocked legacy auth, geo-fenced sign-ins, Defender for Office 365, and DMARC enforcement at p=reject. Cloud Hardened only exists on tenants we provision through our Pax8 channel, because those controls have to live where the identity lives.
What is Huntress and why is it in your stack?
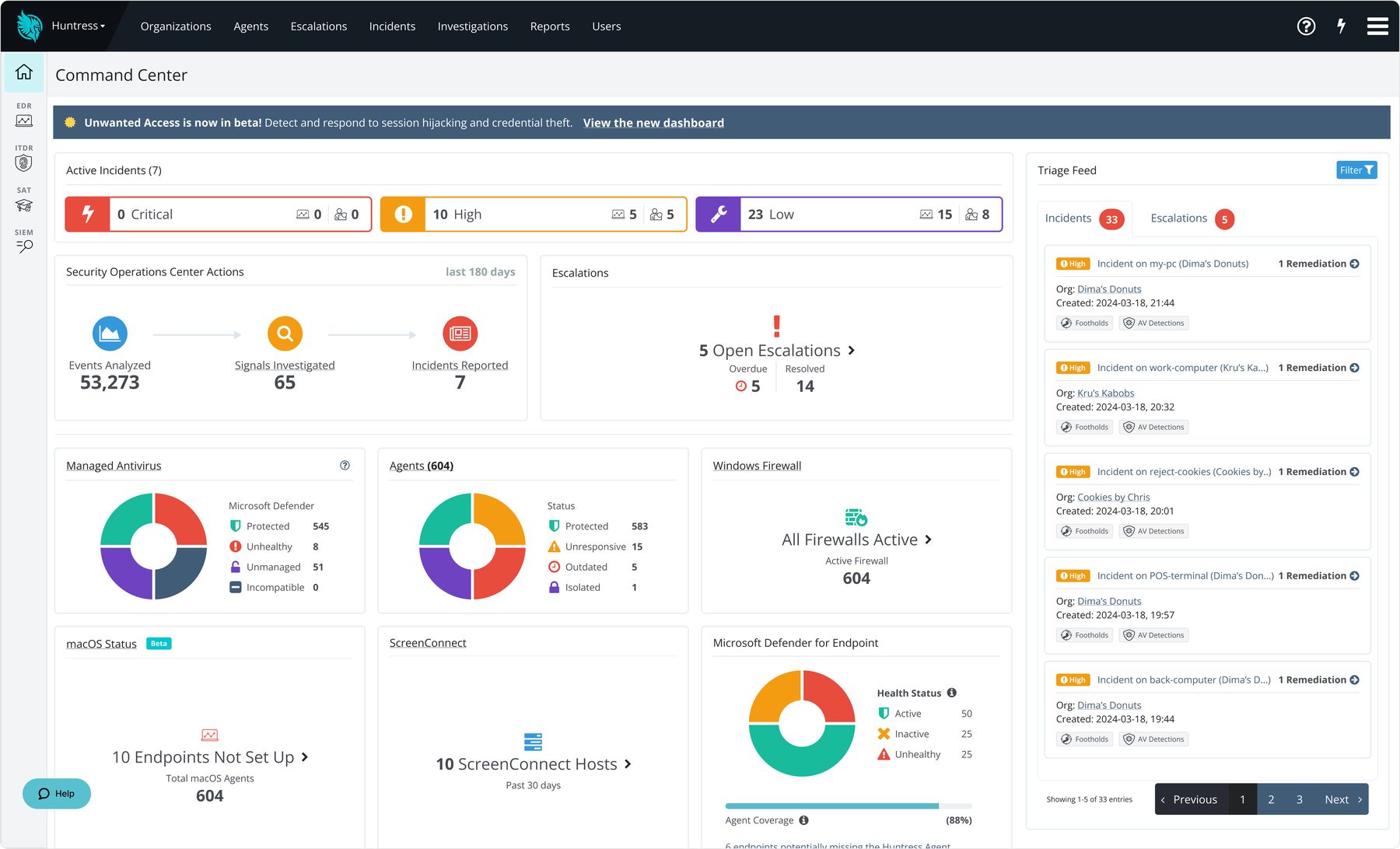
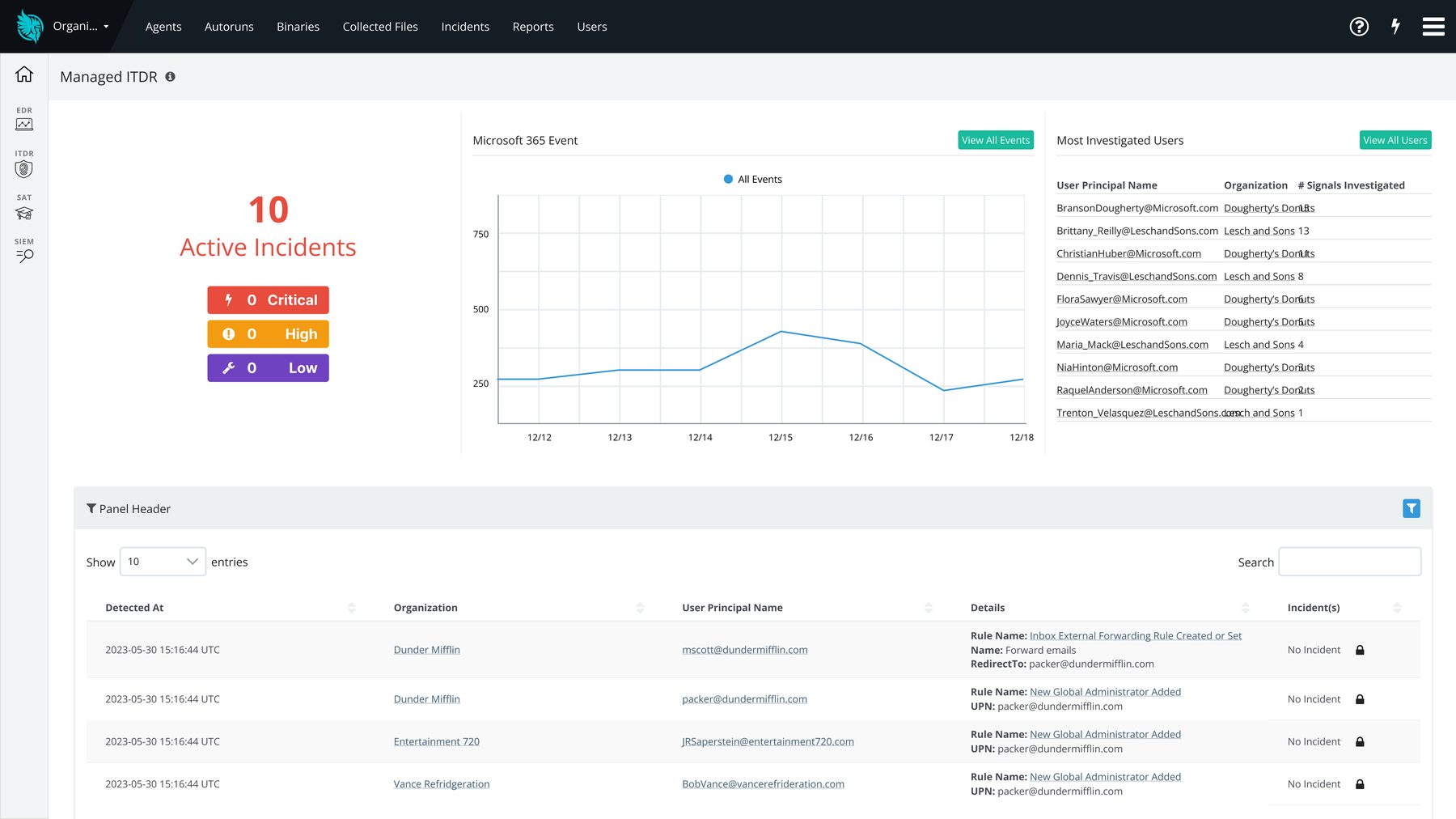
Huntress is a Managed EDR (Endpoint Detection and Response) and ITDR (Identity Threat Detection and Response) platform with a 24/7 human Security Operations Center watching the alerts. Antivirus catches known-bad files. EDR catches the behavior — process injection, persistence mechanisms, ransomware staging — that comes before the payload runs. We're an Authorized Huntress MSP Partner, and Huntress is bundled into every per-user plan from Co-Managed up, and into the Business Shield and Business Fortress flat-rate plans on the Small Business track.
Isn't Microsoft Defender good enough on its own?
Defender out of the box is fine. Defender configured correctly is a serious enterprise-grade product. We harden it to CIS Benchmark Level 1, layer on the 16 ASR rules Microsoft documents but most shops never enable, turn on Tamper Protection, and enroll it in cloud-delivered protection — then add Huntress on top because Defender's own blind spots (identity-layer attacks, living-off-the-land binaries, attacker dwell time) are exactly what a 24/7 SOC is for. The full breakdown is in our blog post "Defender Is Free. Configuring It Correctly Is the Work."
We're a small shop with only a few devices. Do we still get the full security stack?
Yes — the security tier you get is set by which plan you're on, not which page you arrived from. On the per-user track (5+ users), Endpoint Hardened plus Huntress 24/7 SOC is included from Co-Managed ($99/user/month) up. On the flat-rate Small Business track for 1–10 device shops, the security baseline is on every tier; Huntress is added on Business Shield ($199/month, up to 7 devices) and Business Fortress ($349/month, up to 10). The Business Watch tier ($99/month, up to 3) is baseline-only — no Huntress.
Can you help us pass a cyber-insurance audit or renewal?
Yes. The questions on a 2026 cyber-insurance application — MFA on email, EDR on endpoints, immutable backup, written incident response plan, security awareness training, no standing local admin, patching cadence — map almost one-to-one onto what's already in our stack. We provide written attestation of every control, the evidence to back it, and a quarterly compliance report. For many businesses this is the deciding factor — a cheaper provider that can't sign off on the controls leaves the business holding the renewal on its own.
What happens if we actually get hit — do you handle incident response?
Yes. The first response is automated: Huntress isolates the endpoint at the network layer and rolls back what it can. From there a real engineer takes over — containment, scope assessment, restoration from immutable backup, root-cause analysis, and the written report you'll need for insurance and legal. Business Fortress includes a 2-hour incident response retainer and a written IR plan. For per-user clients, IR is covered under your monthly fee for in-scope environments.